Sentinal Backup and Security Control Plane
A professional-grade platform that centralizes MySQL backup orchestration, verification evidence, and security monitoring across distributed Ubuntu servers.
Audience
Decision makers, IT leadership, operations, and compliance stakeholders.
Purpose
Replace ad-hoc scripts with verified, policy-driven backup execution.
Outcome
Trusted backups, faster response time, clear governance.
Enterprise-grade environments
Sentinal is designed for modern data centers and distributed operations teams that manage critical workloads. The platform mirrors enterprise workflows with clear accountability and evidence.


What is Sentinal?
Sentinal provides a unified command center for database continuity and security risk detection. It brings backup policies, execution evidence, and response controls into a single operational plane.
- Designed for multi-server MySQL environments on Ubuntu.
- Backups are verifiable, traceable, and exportable.
- Security telemetry informs backup decisions and quarantines.
Objective of the Portal
Deliver predictable recovery and security governance. Sentinal ensures every backup can be validated, every policy is enforced, and every security anomaly is visible.
Reliability
Consistent automation with clear pass or fail visibility.
Assurance
Verification artifacts for audits and compliance reviews.
Security
Log monitoring, alerting, and quarantine actions.
End-to-End Backup Framework
Sentinal automates backups via SSH and mysqldump, compresses artifacts, routes storage targets, and generates verification evidence in one unified workflow.
Verification Evidence, Not Just Logs
Each run captures database lists, table counts, checksum samples, and SHA256 fingerprints. This elevates backup reporting from success logs to audit-grade evidence.
Database-level visibility
Know exactly which databases were included.
Integrity checks
Checksum sampling detects silent data drift.
Exportable reports
Evidence can be shared with auditors and leadership.
Multi-Target Storage Strategy
Sentinal supports three parallel storage destinations: on the VPS, on the Sentinal host, and on an offsite Ubuntu server. Each tier serves a distinct recovery objective.
Local VPS
Fastest restore for operational incidents.
Sentinal Host
Central archive for compliance and reporting.
Offsite Ubuntu
Disaster recovery and resilience.
Security Monitoring Built In
Sentinal inspects SSH authentication logs to detect failed logins, brute-force patterns, and unauthorized access. Security events are visible alongside backup operations.
Real-time alerts
Immediate visibility into suspicious access attempts.
Quarantine controls
Stop backups to prevent data exfiltration.
SMTP notifications
Send alerts directly to security teams.
Breach Detection as a First-Class Signal
Sentinal elevates breach detection to a core platform capability. High-severity events trigger escalation, highlight compromised servers, and enable immediate quarantine.
High-severity alerts
Root logins, brute-force spikes, and sensor blind spots are flagged instantly.
Operational containment
Quarantine stops backups from running on a potentially compromised host.
Executive visibility
Clear breach timelines help stakeholders understand security posture.
Operational Automation
Scheduled backups run under Celery Beat even when no users are logged in. Retention policies automatically prune old backups to control storage cost.
Scheduling
Hourly, daily, weekly, monthly, or cron-based schedules.
Retention
Automatic cleanup of old backups with configurable limits.
Fallback execution
Local fallback if the broker is temporarily unavailable.
Reporting and Compliance Evidence
Sentinal produces exportable reports that combine backup history, verification artifacts, and breach indicators to support audits and executive reporting.
Backup history export
Includes durations, file sizes, verification results, and storage paths.
Verification proof
Checksums, database lists, and SHA256 signatures demonstrate integrity.
Security timeline
Alerts and breach events can be shared with security leadership.
Cloud and infrastructure alignment
Sentinal integrates with common infrastructure layers. The platform spans application, platform, and infrastructure layers to keep backup and security decisions close to the data.
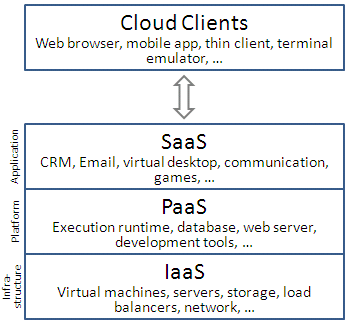
Alignment
Fits into existing IaaS and PaaS environments without re-architecting workloads.
Value
Evidence and monitoring live where infrastructure teams already operate.
Why Decision Makers Choose Sentinal
Sentinal is designed for leadership confidence: it reduces operational risk, increases audit readiness, and improves recovery assurance without adding manual overhead.
Risk reduction
Fewer backup blind spots, better incident response.
Governance
Clear policies and evidence trails for compliance.
Efficiency
Automation frees teams for higher-value work.
Prerequisites and Safe Rollout
Sentinal fits into standard Ubuntu and MySQL environments. A staged rollout ensures operational stability while scaling to production.
Infrastructure
Ubuntu host, Redis, and MySQL credentials with system table access.
Security
SSH host key fingerprints validated out of band.
Rollout plan
Start with staging, validate backups, then scale to production.
Sentinal in one sentence
Sentinal is the enterprise backup and security platform that turns backup operations into verified, auditable, and secure workflows.
